How to Build a Backup Plan
That Actually Survives a Ransomware Attack
A practical guide for Malaysian businesses: the 3-2-1-1 rule, what to test, and how to know your recovery plan will work when it matters most.
The Businesses That Recover Fast Have One Thing in Common
When a ransomware attack hits a Malaysian business, recovery speed is not determined by how much the company spent on security. It is determined almost entirely by how well their backup plan was designed and, more importantly, whether it was ever properly tested.
The difference between a business that resumes operations in 24 hours and one that is still trying to recover three weeks later often comes down to four specific backup decisions made long before the attack. This post covers exactly those decisions, framed as a practical readiness check you can work through with your IT team today.
WHY BACKUP READINESS IS THE DEFINING FACTOR IN 2026
Malaysian businesses faced a 42% year-on-year rise in ransomware attacks in 2025, according to CyberSecurity Malaysia’s Annual Report 2025. The Simply Data Malaysia Cybersecurity Landscape 2026 report confirms that one of the key reasons Malaysian SMEs struggle to recover is simple: many lack properly structured backups.
Ransomware attackers now follow a deliberate playbook: they spend weeks or months inside a network before triggering encryption, and during that time, they specifically target and corrupt backup systems.
Source: Simply Data
The global picture reinforces this. Research from Trilio (November 2025) shows that two-thirds of organisations globally faced ransomware in the past two years, with attackers specifically hunting backup infrastructure to eliminate recovery options. According to BlackFog’s January 2026 analysis, 85% of all ransomware attacks go unreported, and many of the attacks that succeed do so specifically because backup systems were not properly isolated or tested.
Sources: TRILIO and Blag Fog
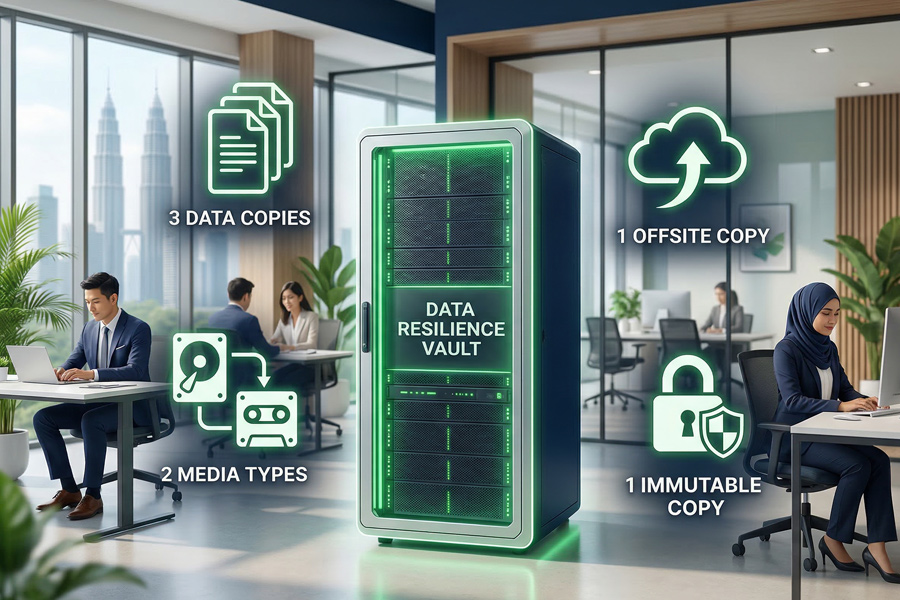
The 3-2-1-1 Rule: The Global Standard for Ransomware-Resistant Backups
3
3 Copies of
Your Data
One production copy plus two backups
2
2 Different
Storage Types
e.g. on-site hardware and cloud
1
1 Offsite Copy
Physically away from your main environment
1
1 Immutable Copy
Cannot be altered or deleted, even by attackers
The fourth number is the critical addition for 2026. An immutable backup is one that is locked in a state that cannot be changed, overwritten, or deleted, even by someone with administrator-level access to your systems. This matters because ransomware attackers with admin access can and will delete or encrypt standard backups. An immutable copy, whether air-gapped (completely disconnected from your network) or stored with object-lock technology in a cloud environment, remains clean regardless of what happens to everything else.
BlackFog’s January 2026 guide frames this directly: a backup strategy built on the 3-2-1-1 rule ensures both redundancy and recovery integrity, even in complex ransomware scenarios where attackers have gained deep network access.
Source: blackfog.com/developing-a-ransomware-backup-strategy
“Ransomware is designed to cause maximum disruption by targeting mission-critical systems. A fast, secure, and reliable backup strategy built on proven principles is one of the most critical components of business continuity. When executed properly, it removes the pressure to pay, even in worst-case scenarios.”
Brenda Robb, Cybersecurity Analyst, BlackFog | January 2026
4 Questions to Test Your Backup Readiness Right Now
Work through these four questions with your IT team or service provider. They directly reflect the backup weaknesses that show up most consistently in Malaysian ransomware incidents, based on CyberSecurity Malaysia incident response data and MYCERT’s Q3 2025 Cyber Incident Report. The answers will tell you clearly where your plan is strong and where it needs attention.
1. Are your backups isolated from your main network?
Ransomware attackers spend an average of weeks inside a network before triggering encryption. During this time, their primary objective is to find and compromise backup systems. If your backups are connected to the same network as your main systems, including through VPN or shared cloud storage credentials, they are at risk. The safest configuration is an air-gapped or immutable backup that has no live connection to your production environment. What to check: Can a person with admin access to your main systems also access and delete your backups? If yes, your backup isolation needs attention.
Source: CISA
If you can answer YES:
Your backups are stored in a separate environment with no direct network connection to your production systems, and backup admin credentials are different from your main system credentials.
If the answer is uncertain:
Ask your IT team: ‘If our main system admin account was compromised, could an attacker also delete our backups?’ If the answer is yes or uncertain, backup isolation should be your next action.
2. When was the last time you actually restored data from your backup and verified it was complete?
A backup that has never been tested is not a backup. It is a hope. Research from Object First (2024) and CISA both confirm this: automated checksums can validate backup integrity, but a full restore drill, actually recovering a system or dataset from backup to a clean environment, is the only reliable way to confirm your recovery will work when you need it. The Rubrik cyber resilience guide puts it plainly: organisations should be able to restore to the most recent clean version of their data in minutes. If your last tested restore happened more than three months ago, the answer to this question is ‘not recently enough.’
Source: Objective First
If you can answer YES:
You can name the date of the last tested restore, the systems that were tested, and the time it took. Your team has a scheduled restore test on the calendar at least quarterly.If the answer is uncertain:
Schedule a restore test this month. Pick one non-critical system and actually restore it from backup. Measure how long it takes. This is your real Recovery Time Objective (RTO), not the estimate.
3. Do you have a defined Recovery Point Objective (RPO) and Recovery Time Objective (RTO) for each critical system?
RPO is the maximum amount of data loss your business can tolerate, measured in time. For example: ‘We can lose up to 4 hours of transaction data but not more.’ RTO is the maximum time your systems can be offline before the impact becomes unacceptable. For most Malaysian SMEs, RPO and RTO targets exist informally but are never written down or tested. The 2026 Ransomware Preparedness Guide from MIPAO Overseas confirms that documented RPO and RTO requirements are must-haves for mission-critical data protection in 2026. Without them, recovery decisions during an incident are made under pressure with no benchmark to measure against.
Source: mipaoverseas.com
If you can answer YES:
Each critical business system has a written RPO and RTO. Your team knows which systems are highest priority for recovery, and your backup schedules are aligned with those RPO targets.If the answer is uncertain:
List your five most critical systems (finance, operations, customer data, communications, inventory) and assign a maximum downtime (RTO) and maximum data loss (RPO) to each. Share this with your IT team and ask whether your current backup schedule meets those targets.
4. Does your written incident response plan include a specific backup recovery procedure, and does your team know their role in the first 30 minutes of an attack?
Research from Druva’s Ransomware Recovery Readiness guide confirms that the first step in any ransomware event is to stop the spread, and that requires knowing immediately which systems are affected and which backup copies are clean. Without a written procedure, teams improvise under pressure, which leads to mistakes including accidentally restoring from a compromised backup copy and reintroducing the ransomware. Microsoft’s Azure security documentation reinforces this: businesses must be able to identify the time frame and details of the attack before choosing which data to recover. The first 30 minutes determine how far the damage spreads.
Source: Druva
If you can answer YES:
A written recovery procedure exists for each critical system. It names specific staff responsible for specific actions. It includes steps for identifying the scope of the attack before beginning restoration. It has been walked through at least once as a tabletop exercise.If the answer is uncertain:
Ask: ‘If ransomware hit us at 9am tomorrow, what would happen in the first 30 minutes?’ If the answer involves uncertainty about who does what, that is your gap. Even a one-page response checklist, printed and placed with your IT team, is meaningfully better than nothing.
The Malaysian Business Reality: Why This Matters Here Specifically
MYCERT’s official Cyber Incident Quarterly Summary Report for Q3 2025 states clearly that good backup management is essential in combating ransomware, and that implementing backup procedures, policies, and best practices is essential for Malaysian organisations. The same report notes that Active Directory servers have become primary targets in Malaysia, regardless of whether they are on-premise or cloud-hosted. This means that even businesses that have moved to cloud environments are not automatically protected if their backup and access controls are not properly configured.
Source: mycert.org.my
For Malaysian SMEs operating under PDPA and the Cybersecurity Act 2024, there is a regulatory dimension as well. Demonstrating that your business can recover personal data and restore data integrity following an incident is part of showing reasonable data protection practice. An untested backup plan, or worse, a backup plan that fails at the moment of a real incident, is a compliance risk as much as an operational one.
The Simply Data Malaysia Cybersecurity Landscape 2026 report confirms a sobering reality for local businesses: ransomware recovery is slow in Malaysia, with many SMEs lacking properly structured backups as a primary reason. The businesses that recover in days rather than weeks are not necessarily larger or better resourced. They are simply better prepared.
YOUR BACKUP READINESS SCORE
4 of 4 answered confidently:
Your backup architecture is solid. Focus on scheduled testing and keeping your RPO and RTO targets current as your business grows.
2 to 3 answered confidently:
Good foundations. Address isolation and testing first, as these have the greatest impact on actual recovery outcomes.
0 to 1 answered confidently:
This is the right moment to have a direct conversation with your IT team or service provider. The gaps are addressable, and starting now is significantly better than starting after an incident.
A Final Word
We encourage every Malaysian business owner to review their backup and recovery readiness with their current IT adviser or service provider. Use the four questions above as a practical starting point. Ask for a written recovery plan that includes defined RPO and RTO targets. Request a scheduled restore test. Ask to see the results of the last one. These are reasonable, professional conversations that any qualified IT partner should welcome.
If you would like a second perspective, or if you are evaluating your options and want an independent view of your backup readiness, BigBand is happy to offer a no-obligation conversation. We are not here to replace your current provider. We are here to make sure your business is as protected as it can be.
FREE BUSINESS TOOL
Cyber Security
Risk Review Checklist
Most organisations are unsure of their actual cyber risk exposure. BigBand’s self-assessment tool evaluates your protection across 7 critical areas and places your organisation into one of four risk levels.