by Tech Voice | Apr 17, 2026 | Cybersecurity, Business Continuity
The RM 3.2 Million Question: Does Your Business Have Cyber Insurance, and Is It Enough? What Malaysian businesses need to know about cyber insurance in 2026 what it covers, what insurers now require before they will issue a policy, and how your security controls...

by Tech Voice | Apr 7, 2026 | Cybersecurity
How Malaysian Manufacturers Can Build a Ransomware-Resilient Operation A five-layer defence guide for production businesses: understanding how attacks unfold, what they cost, and the practical steps that keep your operations running. The Manufacturers That Stay...

by edward | Apr 4, 2026 | News & Update, Cloud, Cybersecurity
The Government Will Help Pay for Your Digital Upgrade. Here Is How to Claim It. A practical guide to the top 3 Malaysia government grants available right now for SME cybersecurity, cloud, and digital infrastructure investment. Most Malaysian SMEs Are Leaving...
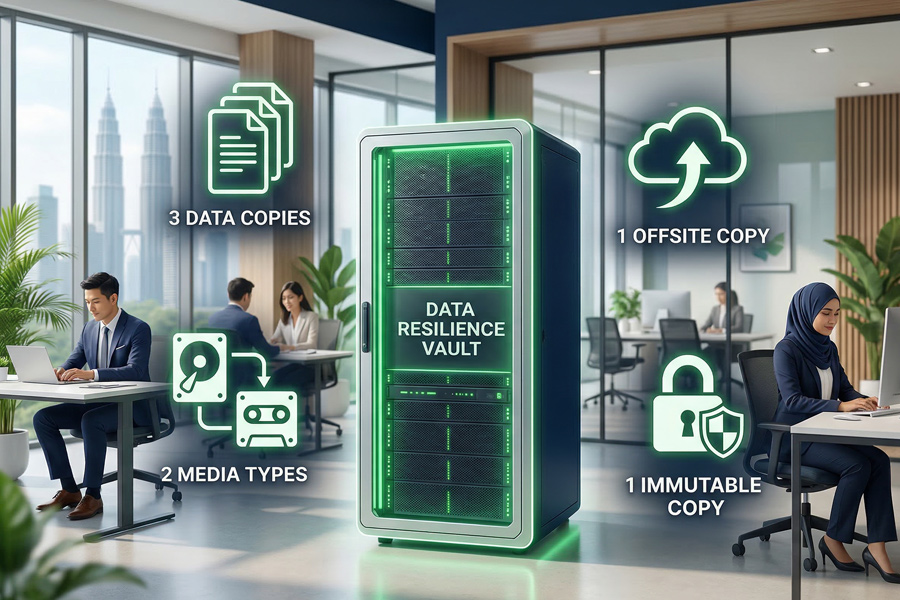
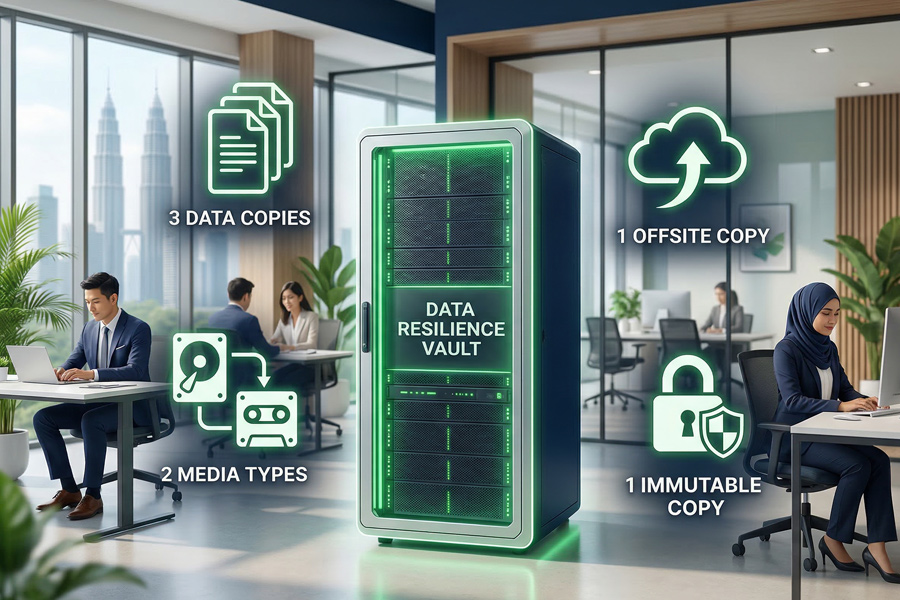
by edward | Apr 2, 2026 | Backup and Recovery, Cybersecurity
How to Build a Backup Plan That Actually Survives a Ransomware Attack A practical guide for Malaysian businesses: the 3-2-1-1 rule, what to test, and how to know your recovery plan will work when it matters most. The Businesses That Recover Fast Have One Thing in...

by edward | Apr 1, 2026 | Cybersecurity
5 Questions Every Malaysian Business Owner Should Ask About Cyber Readiness Today A practical guide to knowing where you stand, before an incident forces the question. The Businesses That Survive Are the Ones That Prepared There is a quiet difference between...

by edward | Mar 27, 2026 | Cybersecurity
Zero Trust: The Security Model Every Malaysian Business Needs in 2026. Your perimeter firewall assumes the threat is outside. In 2026, it is already inside. 🚨 The Threat That Was Already Inside Your firewall is active. Your antivirus is updated. Your staff have been...